In an ongoing hack that started earlier this month, threat actors have actively compromised over 130 organizations through Twilio, exposing the credentials of close to 10,000 employees.
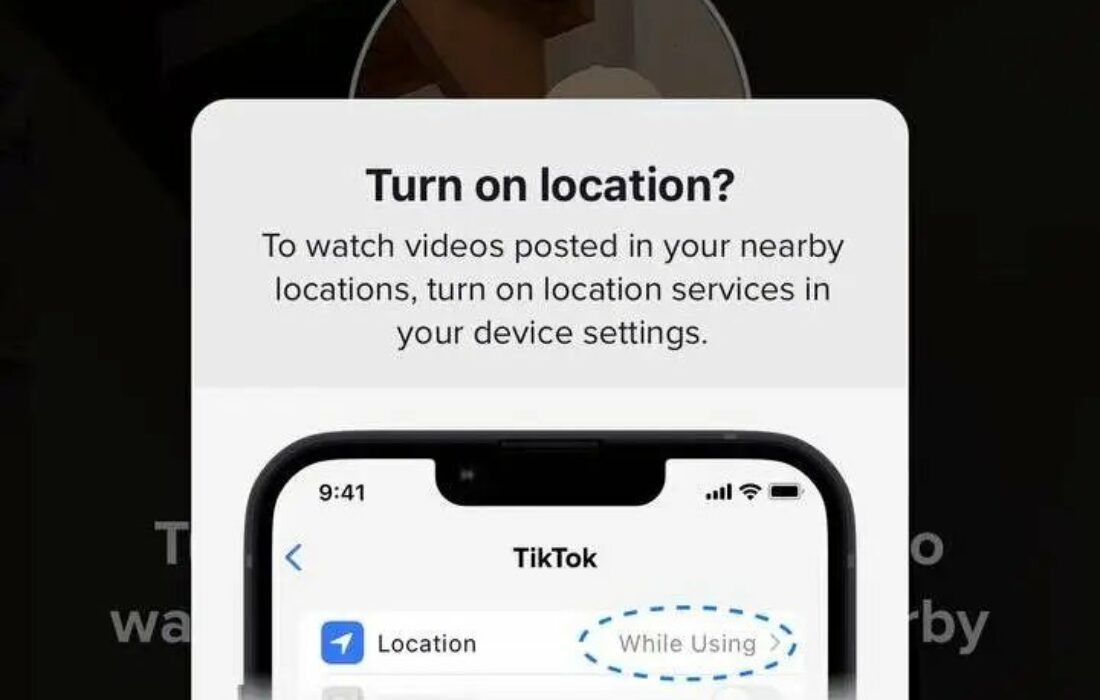
The hackers tricked employees into handing over their corporate login credentials and two-factor codes using SMS phishing messages that claimed to be Twilio’s IT department.
Cybersecurity company Group-IB says the attack on Twilio was part of a wider campaign by the “0ktapus” hacking group, a name signifying how they predominantly hack organizations using Okta as a single sign-on provider.
Since March, the hackers have taken over at least 9,931 user credentials, more than half of which were captured using multi-factor authentication codes that were used to access a company’s network.
Group-IB launched an investigation after one of its customers was targeted by a linked phishing attack, and found that the majority of the targeted companies were headquartered in the U.S. or have U.S.-based staff.
The hacker’s phishing kit also revealed configuration details of the Telegram bot that the attackers used to drop compromised data. Through this discovery, Group-IB successfully identified one of the Telegram group’s administrators, “X,” whose GitHub and Twitter handles suggest they may reside in North Carolina.
Although it’s not clear how the attackers compiled the names and phone numbers of the victims, Group-IB speculates that the attacker who first targeted mobile operators and telecommunications companies “could have collected the numbers from those initial attacks.”
In a statement to TechCrunch, Roberto Martinez, a senior threat intelligence analyst at Group-IB, explained: “On many occasions, there are images, fonts, or scripts that are unique enough that they can be used to identify phishing websites designed with the same phishing kit. In this case, we found an image that is legitimately used by sites leveraging Okta authentication, being used by the phishing kit.”
He continued: “Once we located a copy of the phishing kit, we started digging deeper to get a better understanding of the threat. The analysis of the phishing kit revealed that it was poorly configured and the way it had been developed provided an ability to extract stolen credentials for further analysis.”
The corporate victims operate in a number of IT, software development and cloud services, including 13 organizations in the finance industry, seven retail giants, and two video game organizations.
Story Update (26 Aug, 22): DoorDash has been hit by the same hackers less than 24 hours later. The hackers took over employee credentials of a third-party vendor that were then used to gain access to some of DoorDash’s internal tools.
DoorDash revealed that the attackers managed to access the names, email addresses, delivery addresses and phone numbers of DoorDash customers. For a “smaller subset” of users, hackers also accessed partial payment card information, including card type and the last four digits of the card number.
If you see something out of place or would like to contribute to this story, check out our Ethics and Policy section.